Day in the Life: What Fintech Engineers Actually Do
It's 2:14am. Your phone screams at you. The PagerDuty alert says: ACH batch file rejected — $40M in payroll stuck. Somewhere, thousands of people are not going to see their direct deposit hit tomorrow morning. You have four hours to fix it before the bank's settlement window closes.
You sit up, pull your laptop onto your lap, and start reading logs.
That is fintech engineering. Not always at 2am — but always with that weight. The code you write moves real money. When it fails, real people feel it. There is no "we'll fix it in the next sprint" when a company's payroll is stuck in transit.
If that scenario sounds terrifying, fintech engineering might not be for you. If some part of you finds it clarifying — a problem that actually matters, with a hard deadline, and real consequences — read on. Because the people who thrive in this field feel the stakes and run toward them anyway.
What Makes Fintech Engineering Different
Before walking through what a day actually looks like, you need to understand why fintech engineering is its own discipline. It is not just "banking with better APIs." The differences run deep.
Money movement means zero tolerance for errors. In a typical SaaS company, a bug that affects 0.1% of users is a low-priority ticket. In a payments system, a bug that affects 0.1% of transactions might mean thousands of people were charged twice, or funds disappeared between accounts. Uptime is not a vanity metric — it is a fiduciary obligation. You build differently when you know that.
Regulations live inside the codebase. Know Your Customer (KYC) checks, Anti-Money Laundering (AML) rules, OFAC sanctions screening, Reg E dispute windows — these are not policy documents that compliance handles. They are code you write and maintain. The audit log for a suspicious transaction cannot be modified. The dispute must be resolved within a legally mandated timeframe. When a regulator asks for records, they come from your database. Engineers who have never worked in fintech often underestimate how much regulatory logic ends up embedded in business-critical code paths.
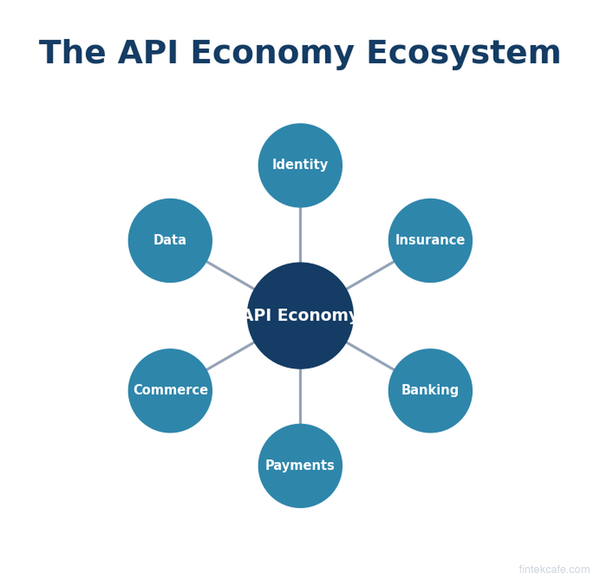
External dependency hell is real and permanent. Your payment stack will touch Visa, Mastercard, FedNow, ACH networks, core banking vendors, card processors, and partner bank APIs. Every single one of them has its own ISO 8583 message format, its own proprietary error codes, its own undocumented quirks, and its own maintenance windows that do not align with yours. They all break differently. You will spend a non-trivial portion of your career decoding cryptic error responses from a Fiserv integration that was last updated in 2009.
Security is not optional and it is not fast. Multi-party computation for key management, HSMs for storing cryptographic keys, PCI-DSS compliance for anything touching card data, SOC 2 audits — the security overhead in fintech is real, it slows things down, and it cannot be skipped. Engineers who want to ship fast and iterate freely often find this friction maddening. Engineers who understand why it exists tend to embrace it as part of the craft.
Three Types of Fintech Engineers — A Realistic Day for Each
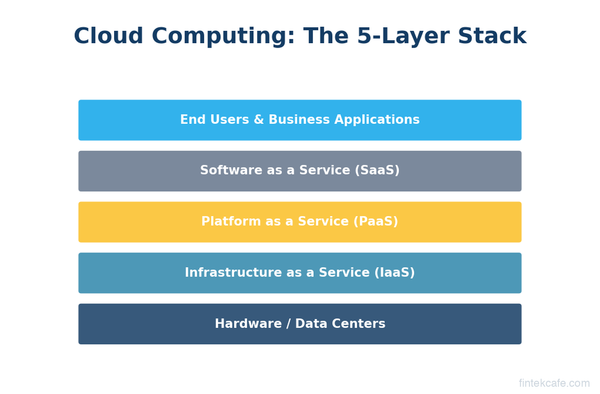
Fintech engineering is not monolithic. The day-to-day experience varies enormously depending on what layer of the stack you work on. Here are three archetypes and what a typical day actually looks like.
The Payments Engineer (Stripe, Adyen, a neobank)
8:45am. You join standup. The team lead mentions that webhook delivery success rate dropped two points overnight. You know immediately what this likely is — a third-party endpoint timing out and triggering the retry queue — but you pull up the logs before saying anything, because in payments, you do not guess.
9:20am. You are right. A merchant's endpoint started returning 504s at 3am, which triggered exponential backoff retries, which is filling the queue, which is now creating latency for unrelated merchants. You write a quick analysis, propose a fix to isolate per-merchant retry queues, and open a PR.
11:00am. Code review on a change to authorization retry logic. Your colleague wants to retry on a specific decline code. You flag it: that decline code means "do not retry — the issuer has flagged this card." Retrying anyway risks triggering velocity checks on the issuer's side and getting your BIN flagged. This is the kind of thing you only know if you have spent time reading Visa and Mastercard technical documentation. You leave a detailed comment and move on.
2:00pm. Writing integration tests for a new card network integration. The test environment behaves slightly differently from production — it always does — and you are building a test harness that simulates the edge cases the documentation does not cover: partial authorizations, network timeouts at the authorization stage, currency conversion edge cases. This takes hours. It should take hours.
4:30pm. Slack message from the fraud team: a specific BIN range is triggering a spike in declines that look unusual. You join a call to cross-reference the payment logs with what fraud is seeing. You are shipping a diagnostic endpoint to help them query transaction patterns without needing direct database access.
What keeps you up at night: a bug in the retry logic that charges customers twice. A race condition in the authorization flow. A webhook that silently fails and leaves a merchant thinking a payment succeeded when it did not.
The Risk and Fraud Engineer (Chime, Nubank, Klarna)
8:30am. You check the dashboard before standup. Fraud model precision dropped slightly overnight. False positive rate is up half a point. Half a point does not sound like much until you remember that each false positive is a real customer whose legitimate transaction got blocked. You make a note to dig in.
9:15am. You find it. A rule you deployed last week — a velocity check on transactions from new devices — is catching a cohort of legitimate users who signed up during a promotional campaign and are all transacting for the first time on new phones. Classic. You adjust the rule to add an account-age exception and deploy to shadow mode, meaning it runs but does not block, so you can measure the impact before it goes live.
11:00am. ML pipeline work. You are engineering a new feature for the fraud model — merchant category code velocity by account. The feature logic is straightforward; the hard part is making sure the feature is computed correctly in both real-time inference and the batch training pipeline, because if they diverge, the model trains on data that does not match what it sees in production. This is called training-serving skew and it is one of the more insidious bugs in applied ML.
2:30pm. A fraud ops analyst flags a new attack pattern: a ring of accounts making small-dollar P2P transfers in a specific graph topology, then cashing out via ACH. You pull the data, write an exploratory query in SQL, and map the network. This is the part of fraud engineering that feels like detective work. You draft a new rule to block the pattern and schedule a review with the ops team.
4:00pm. Coordination call with compliance. A regulator has asked about the company's AML transaction monitoring methodology. You walk them through the logic of two rules and explain the tuning rationale. You are not a lawyer. But you need to be able to explain your code to one.
What keeps you up at night: blocking a legitimate customer at a critical moment — their rent payment, their payroll deposit. Missing an attack pattern until it has already cost $2M in losses.
The Platform and Infrastructure Engineer at a Neobank
This is the least glamorous role in fintech and arguably the most important. You are building the ledger. The transaction processing pipeline. The partner bank integrations that make all of it work.
9:00am. Standup, then straight into a migration. You are moving the core ledger service from one database cluster to another, zero-downtime. You have been planning this for six weeks. Today is the cutover day. The runbook is forty steps long. You have a rollback plan. You still feel nervous.
11:00am. You receive a Slack from a colleague: the Galileo API just changed the response format for a balance endpoint — without notice, which is par for the course with core banking middleware providers. You have fifteen minutes to write a patch before it breaks balance checks for new card activations. You write it in ten, test it in four, deploy it in one.
1:30pm. Reviewing a PR for the transaction processing pipeline. A new engineer has introduced a subtle race condition: two concurrent transactions against the same account could, under specific timing conditions, result in a negative balance that should not be allowed. You catch it, explain it in the review, and pair with them after standup to redesign the locking strategy.
3:30pm. Writing a runbook for on-call. What do you do if the FedNow integration goes down? Who do you call at the partner bank? What is the escalation path? What transactions need to be reprocessed and in what order? This is not exciting work. It is essential work, and it is what makes the difference between a two-hour outage and an eight-hour outage.
What keeps you up at night: the ledger being wrong. Not system downtime — ledger inconsistency. Money appearing or disappearing from accounts that should not be affected by a failure. Double-spend bugs. The kinds of errors that can take days to reconcile and cost the company its banking charter if they go undetected.
The On-Call Reality
On-call in fintech is different from on-call at a typical SaaS company. The incidents have more urgency, the blast radius is more concrete, and the recovery is often more complex.
A typical fintech incident is not "the dashboard is slow." It is: a payment processing delay is causing a backlog of unconfirmed transactions; a settlement file failed to post and funds are in limbo; a fraud model started blocking 40% of transactions because a feature pipeline broke and is serving null values; a partner bank's API is returning 503s and ACH origination is halted.
Incident response in fintech has a rhythm: detect, assess impact in dollars and accounts affected, contain, fix, communicate (to ops teams, to compliance, sometimes to regulators), and write a postmortem with enough detail that it cannot happen again. The postmortem is not optional. The audit trail of what happened and why is a regulatory artifact.
The upside: when you fix it, you actually fixed something that mattered.
What You Need to Succeed as a Fintech Engineer
| Skill | Payments Engineer | Risk & Fraud Engineer | Platform Engineer |
|---|---|---|---|
| Payment rail knowledge (ACH, card networks, wires) | Essential | Helpful | Essential |
| Distributed systems / eventual consistency | Essential | Helpful | Essential |
| SQL and data querying | Helpful | Essential | Helpful |
| ML / statistical reasoning | Not required | Essential | Not required |
| Regulatory awareness (KYC, AML, Reg E) | Important | Important | Important |
| External API integration experience | Essential | Helpful | Essential |
| Security mindset (PCI-DSS, encryption) | Essential | Important | Essential |
| On-call / incident response comfort | Essential | Important | Essential |
Beyond the table: the single most underrated skill in fintech engineering is the ability to read financial regulations well enough to translate them into code requirements. You do not need a law degree. You need to read a 40-page Fed Regulation E document, identify the 12 rules that affect your dispute processing flow, and turn them into acceptance criteria. Most engineers find this painful at first. The ones who get good at it become indispensable.
Paranoia about data integrity is not optional. It is a professional requirement. If you write a ledger update that does not account for what happens if the server crashes midway through — between the debit and the credit — you are not a careful enough engineer for this environment. Idempotency keys, two-phase commits, compensating transactions: these are not advanced topics in fintech, they are table stakes.
Is Fintech Engineering Right for You?
Here is an honest breakdown.
You will thrive in fintech engineering if you are detail-oriented to the point of being annoying about it. If you naturally ask "what happens if this fails halfway through?" You like understanding how systems connect, not just your own service. You find the intersection of regulation and technology interesting rather than irritating. You want your work to have real stakes — not manufactured urgency, but genuine consequence.
You will struggle in fintech if you want to move fast and break things. That phrase is not a philosophy that maps onto financial systems — it is a liability. If you find compliance overhead suffocating rather than clarifying, if you want to spend most of your time on greenfield product work rather than deeply understanding external constraints, or if incident response feels like punishment rather than part of the job — fintech will grind you down.
The engineers who love this field tend to describe it the same way: it is hard, it matters, and when something goes wrong, fixing it actually feels like fixing something. The ACH batch at 2am. The fraud attack you shut down before it scaled. The ledger migration that went flawlessly because you wrote a 40-step runbook and tested it twice.
The code moves money. That is the point.
Key Takeaways
- Fintech engineering is differentiated by regulatory constraints in the codebase, zero tolerance for data integrity failures, and permanent dependence on external payment rail APIs that break in unpredictable ways.
- The three main engineering archetypes — payments, risk/fraud, and platform/infrastructure — have meaningfully different day-to-day experiences and require different technical emphases.
- On-call in fintech carries real stakes: incidents affect real people's money and must be documented thoroughly for regulatory purposes.
- The most underrated skill in fintech engineering is reading financial regulations closely enough to translate them into code requirements.
- Engineers who thrive here are detail-oriented, comfortable with compliance overhead, and energized by real consequence; those who find this friction stifling are better served by other domains.
- Compensation in fintech engineering is strong — particularly at neobanks and infrastructure-layer companies — because the complexity and responsibility are genuinely higher than in most SaaS roles.
Related Reading
- How ACH Payments Work — The technical mechanics behind the payment rail that shows up in nearly every fintech stack.
- How to Get Into Fintech — A roadmap for engineers and career changers trying to break into the industry.
- Fraud Detection System Architecture — A deep dive into how modern fraud detection pipelines are built and tuned.